Enterprise-Grade Security. Responsible AI by Design.
From encrypted infrastructure to tightly scoped LLM usage, your data is always protected, never exposed and never used to train models.
Data Security & Responsible Use of LLMs
We understand that mechanical and electrical drawings are highly confidential and often represent a firm’s most sensitive intellectual property. Data security is therefore a first-class design principle in our platform.
Four Pillars of Trust
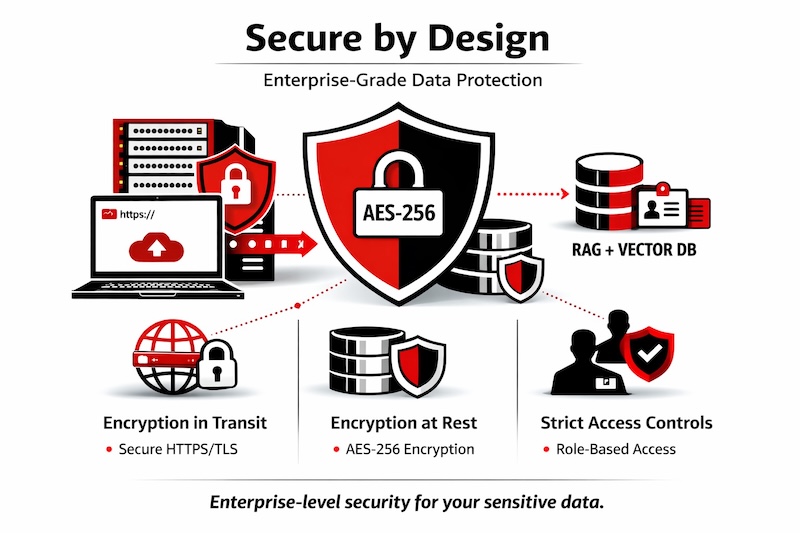
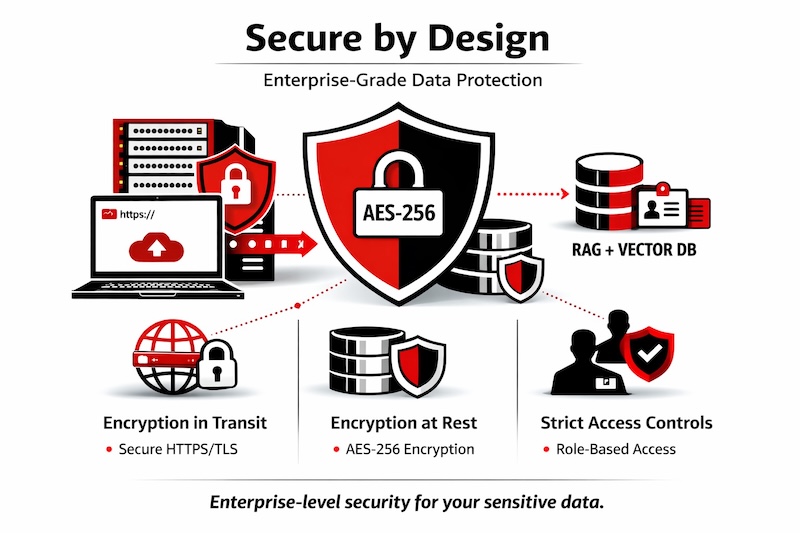
1. Secure by Design
We follow enterprise-grade security best practices to protect your data at every stage:
- Encryption in Transit
All data is transmitted over secure HTTPS/TLS channels, protecting it during upload, processing, and access. - Encryption at Rest
All stored data including drawings, extracted metadata, and intermediate artifacts is encrypted using industry-standard AES-256. - Strict Access Controls
Role-based access ensures data is only available on a need-to-know basis, with full auditability.
Aligned with modern enterprise SaaS security expectations for handling sensitive IP.
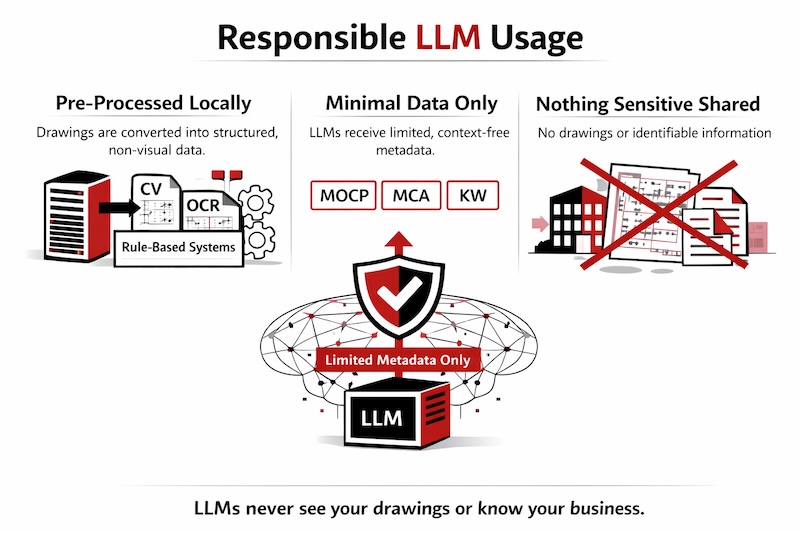
2. Responsible LLM Usage
- Pre-Processed Locally
Drawings are converted into structured, non-visual data using CV, OCR, and rule-based systems before any LLM is used. - Minimal Data Only
LLMs receive limited, context-free metadata (e.g., MOCP, MCA, kW, HP). - Nothing Sensitive Shared
No drawings, images, title blocks, company names, or identifiable project data are ever sent.
LLMs never see your drawings or know your business.
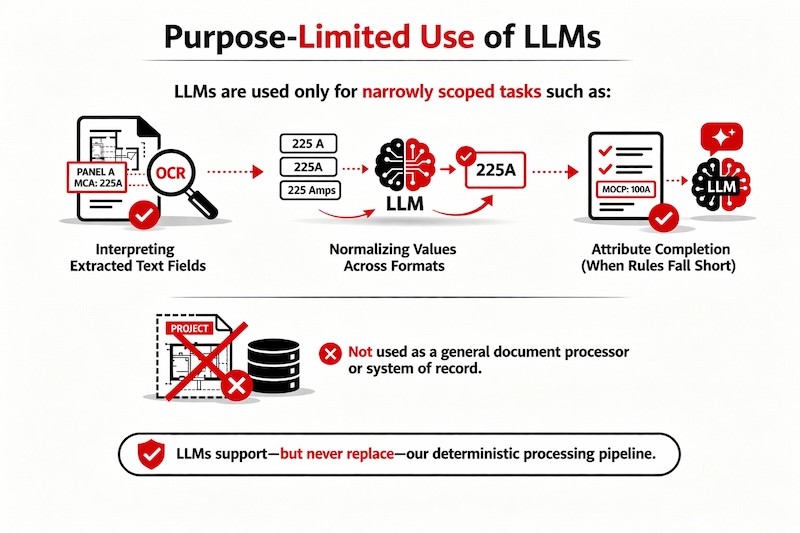
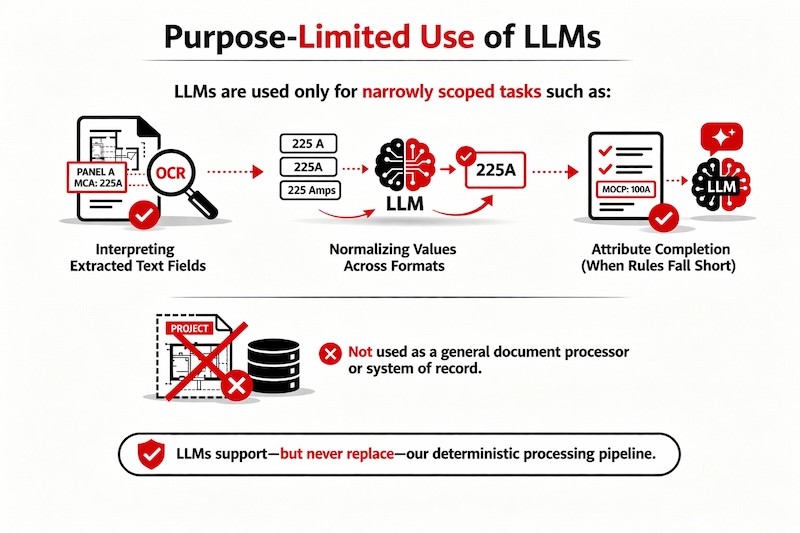
3. Purpose-Limited Use of LLMs
LLMs are used only for narrowly scoped tasks such as:
- Interpreting extracted text fields
- Normalizing values across formats
- Assisting with attribute completion where rules alone are insufficient
They are not used as a general document processor or as a system of record.
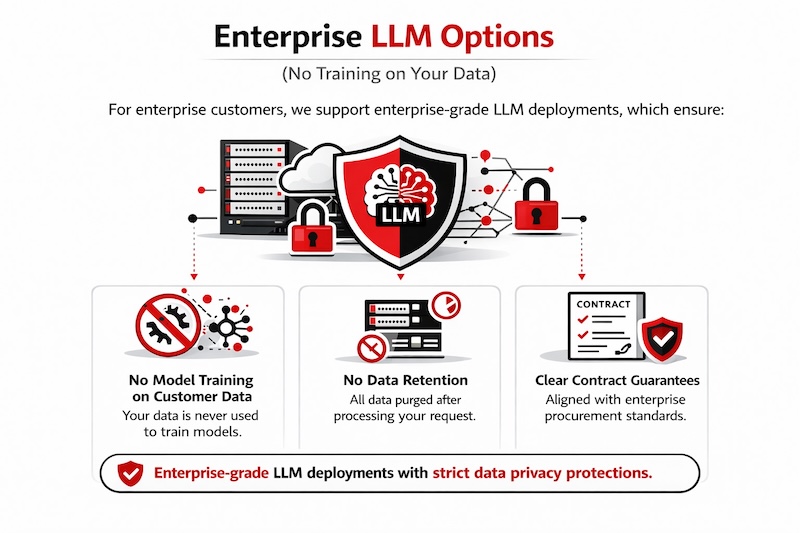
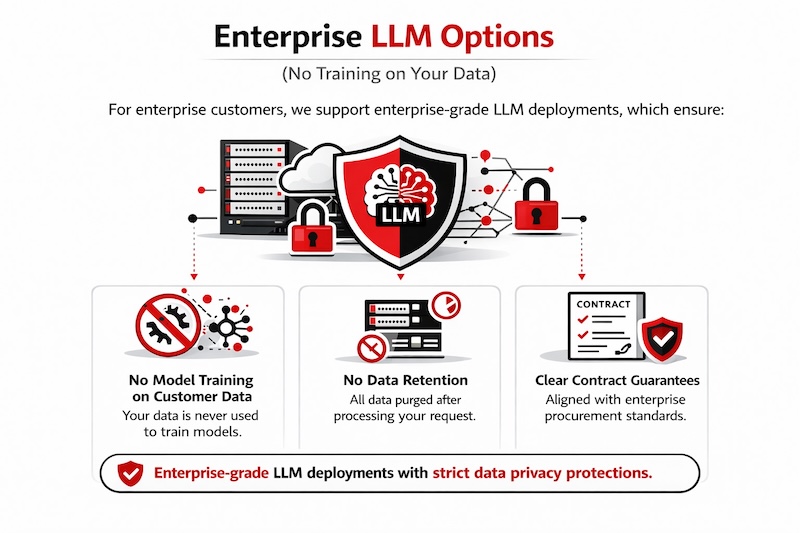
4. Enterprise LLM Options (No Training on Your Data)
For enterprise customers, we support enterprise-grade LLM deployments, which ensure:
- No customer data is used for model training
- No data retention beyond request processing
- Clear contractual guarantees aligned with enterprise procurement standards
This applies even to the limited metadata that may be sent for inference
1. Secure by Design
We follow enterprise-grade security best practices to protect your data at every stage:
- Encryption in Transit
All data is transmitted over secure HTTPS/TLS channels, protecting it during upload, processing, and access. - Encryption at Rest
All stored data including drawings, extracted metadata, and intermediate artifacts is encrypted using industry-standard AES-256. - Strict Access Controls
Role-based access ensures data is only available on a need-to-know basis, with full auditability.
Aligned with modern enterprise SaaS security expectations for handling sensitive IP.
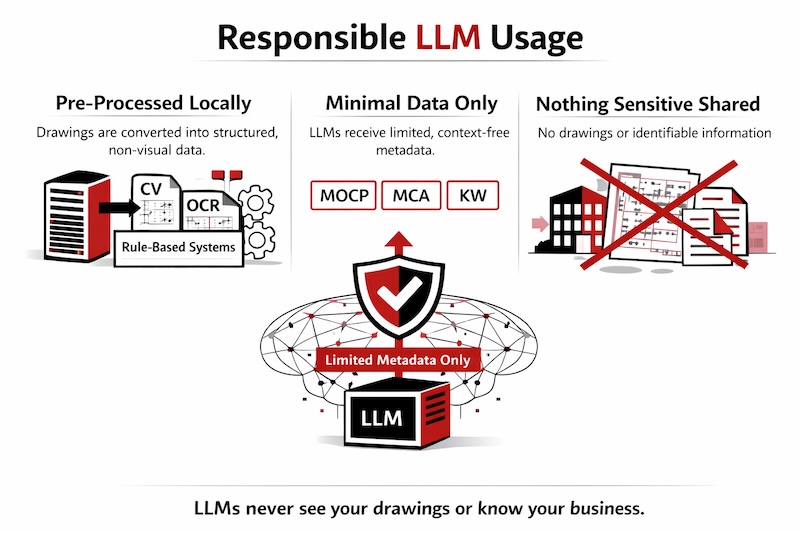
2. Responsible LLM Usage
- Pre-Processed Locally
Drawings are converted into structured, non-visual data using CV, OCR, and rule-based systems before any LLM is used. - Minimal Data Only
LLMs receive limited, context-free metadata (e.g., MOCP, MCA, kW, HP). - Nothing Sensitive Shared
No drawings, images, title blocks, company names, or identifiable project data are ever sent.
LLMs never see your drawings or know your business.
3. Purpose-Limited Use of LLMs
LLMs are used only for narrowly scoped tasks such as:
- Interpreting extracted text fields
- Normalizing values across formats
- Assisting with attribute completion where rules alone are insufficient
They are not used as a general document processor or as a system of record.
4. Enterprise LLM Options (No Training on Your Data)
For enterprise customers, we support enterprise-grade LLM deployments, which ensure:
- No customer data is used for model training
- No data retention beyond request processing
- Clear contractual guarantees aligned with enterprise procurement standards
This applies even to the limited metadata that may be sent for inference